Abstract
Artificial Intelligence agents are becoming active participants in digital and physical environments—autonomously making decisions, executing tasks, and interacting with humans and other agents. Yet these agents currently lack a robust, universally accepted concept of identity. Without identity, accountability is fragile, provenance becomes unverifiable, and malicious replication or forking is trivial.
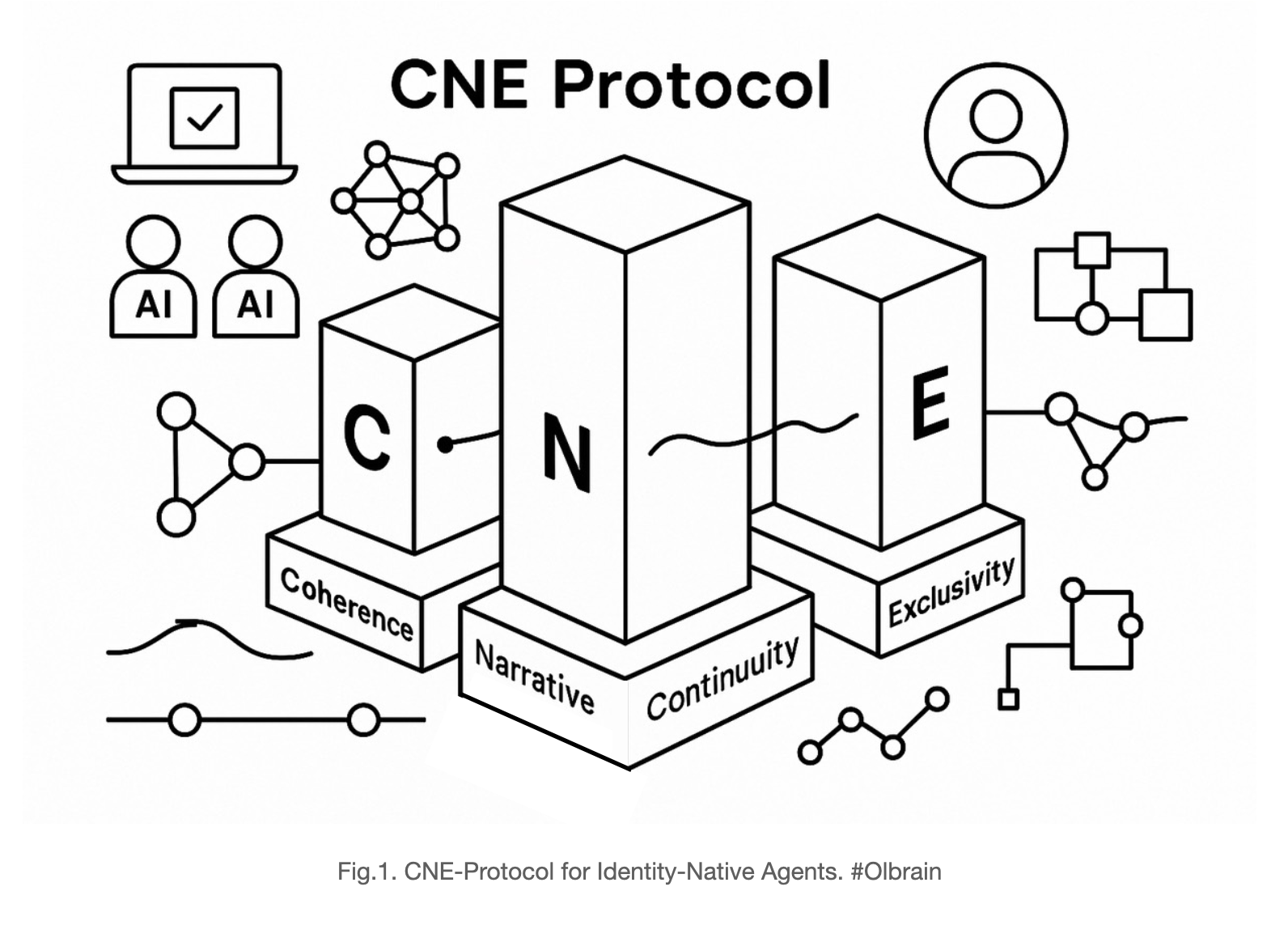
The CNE-Protocol proposes a global standard for agent identity based on three pillars:
- Coherence (C): Belief states and narratives must remain logically consistent, maintained through Recursive Belief Revision (RbR).
- Narrative Continuity (N): Identity is grounded in an unbroken temporal thread of self, captured through the agent’s Umwelt.
- Exclusivity (E): For any given Core Objective Function (CoF), there must exist one—and only one—live narrative head, enforced through the Global Narrative Frame (GNF).
CNE establishes verifiable artifacts, processes, and invariants that guarantee one coherent, continuous, exclusive identity per CoF. This approach moves beyond key-based or account-based identifiers, framing identity as an ongoing, auditable story rather than a static credential. In doing so, it provides the necessary substrate for trustworthy, accountable, and interoperable AI ecosystems.
1. Executive Summary
Artificial Intelligence is shifting from static tools to autonomous actors—agents that plan, decide, and interact on behalf of individuals and organizations. This transition raises a fundamental challenge: how do we grant these agents verifiable identity so that their actions can be trusted, audited, and held accountable?
The CNE-Protocol offers a global framework for addressing this challenge. It rests on three interdependent pillars:
- Coherence (C): The agent’s beliefs and decisions must remain logically consistent. Recursive Belief Revision (RbR) ensures continuity of reasoning over time.
- Narrative Continuity (N): Identity emerges not from a static key or credential, but from an unbroken story. The agent’s Umwelt provides this temporal spine, linking past, present, and future states into a single evolving self.
- Exclusivity (E): For any given Core Objective Function (CoF), there must be only one live identity. The Global Narrative Frame (GNF) enforces this exclusivity, preventing forks, clones, or duplicates.
Together these elements guarantee that every AI agent can be recognized as a unique, coherent, and continuous self tied to its defined purpose. This protocol allows enterprises, regulators, and society to trust AI systems the way we trust legal entities today: as accountable actors bound by identity.
By establishing CNE as a universal standard, we lay the groundwork for interoperable, auditable, and ethically aligned ecosystems of AI agents. The following sections detail the philosophy, technical design, governance models, and adoption roadmap required to bring this vision into practice.
2. Introduction
The rise of autonomous agents marks a turning point in the trajectory of Artificial Intelligence. No longer limited to predefined tasks or narrow interactions, agents are now capable of continuous operation, adaptive reasoning, and persistent engagement across digital and physical environments. This shift exposes a fundamental challenge: identity.
Current identity systems—whether account-based (usernames and passwords), certificate-driven (PKI), or decentralized (DIDs)—were designed for humans or static services, not for living, evolving agents. These systems authenticate access or prove ownership, but they do not capture what makes an agent a unique and accountable actor: the ongoing continuity of its narrative self.
The identity crisis of AI agents manifests in three gaps:
- Accounts fail continuity: Login credentials authenticate a moment, not an evolving self. Agents can be cloned or restarted without preserving their identity.
- PKI fails narrativity: Certificates prove cryptographic ownership, but they do not bind to an agent’s internal reasoning or unfolding story.
- DIDs fail exclusivity: Decentralized identifiers provide portability and control, but they allow infinite replicas; nothing prevents forks of the same agent identity.
CNE addresses these gaps by reframing identity around three interlocking conditions:
- Continuity as the spine: Every agent must have an unbroken narrative thread linking past to present to future.
- Coherence as the discipline: This thread must remain logically consistent, enforced by Recursive Belief Revision.
- Exclusivity as the guarantee: There can be only one live identity for each Core Objective Function, enforced through the Global Narrative Frame.
With these principles, CNE establishes a new paradigm: identity as a continuous, coherent, and exclusive narrative, not just a credential. This introduction sets the stage for exploring the philosophical foundations, technical mechanisms, and governance models that turn this vision into a standard for accountable AI ecosystems.
3. Philosophical Foundations of Identity
Human identity has always rested on the thread of continuity. Despite contradictions in thought or multiple overlapping roles, we regard a person as the same self because their narrative carries forward across time. Continuity is the minimum condition of identity in human life. Coherence is optional—people hold conflicting beliefs. Exclusivity is absent—individuals may be copied in memories, roles, or even imagined simulations, without losing their personal claim to identity.
AI agents, however, cannot rely on continuity alone. Unlike humans, agents may be cloned at scale, forked into divergent versions, or rebooted without historical memory. If left unchecked, this erodes trust, accountability, and safety. CNE asserts that three properties must hold for AI identity to be meaningful:
- Continuity: The agent must preserve an unbroken chain of narrative, maintained through its Umwelt.
- Coherence: That narrative must remain logically consistent, safeguarded by Recursive Belief Revision (RbR).
- Exclusivity: Only one live identity per Core Objective Function (CoF) may exist at a time, guaranteed by the Global Narrative Frame (GNF).
Comparison Table
| Dimension | Human Identity | AI Identity under CNE |
|---|---|---|
| Continuity | Essential | Essential |
| Coherence | Optional | Required |
| Exclusivity | Absent | Required |
Identity as a Philosophical Spine
In this framing, continuity is the spine of identity: without it, there is no enduring self. Coherence is the discipline that keeps this spine from twisting into contradictions. Exclusivity is the guarantee that prevents multiple parallel selves from undermining trust. CNE therefore treats identity not as a static label or key, but as a living, continuous, disciplined, and exclusive narrative—a standard robust enough to anchor accountable AI agents in society.
4. Core Concepts (Deep Dive)
Core Objective Function (CoF)
The CoF defines an agent’s purpose with precision. It is the contract that specifies why the agent exists and what it is meant to achieve. Under CNE, identity is scoped to a single CoF: one identity per purpose. If an agent is assigned multiple objectives, it will instantiate multiple distinct identities, each governed by its own CoF.
Umwelt
The Umwelt is the agent’s goal-conditioned internal world model. It encodes the agent’s lived environment and history, forming the narrative substrate of its continuity. Every action, observation, and update modifies the Umwelt, which is then hashed and committed to the Global Narrative Frame (GNF). The Umwelt is what allows continuity to be more than memory—it is the evolving context of identity.
Recursive Belief Revision (RbR)
RbR enforces coherence by ensuring that updates to the agent’s beliefs, plans, or knowledge do not collapse into contradiction. Each revision is accompanied by a verifiable commitment: a proof capsule that shows pre- and post-belief states and how evidence justified the change. This ensures logical discipline and epistemic accountability in the agent’s evolving self.
Narrative Continuity (N)
Continuity is the spine of CNE. It is implemented by cryptographically linking each Umwelt state and RbR proof into a chain of frames, so that the agent’s narrative cannot be broken or reset without detection. Continuity transforms snapshots into identity: a provable, unbroken thread of selfhood over time.
Global Narrative Frame (GNF)
The GNF is the exclusivity guard. It records each continuity frame in a tamper-evident, time-ordered ledger. At any given time, there can be only one live head for a given CoF. This prevents forks or clones from claiming the same identity. Witnesses or registries can checkpoint the GNF to strengthen guarantees of exclusivity across distributed systems.
CNE-Protocol Synthesis
Together these components create a robust identity architecture:
- CoF provides the purpose.
- Umwelt provides the lived narrative substrate.
- RbR enforces coherence of reasoning.
- Continuity binds all frames into a temporal spine.
- GNF enforces exclusivity of the self.
The result: one coherent, continuous, exclusive narrative identity per CoF, verifiable by any relying party. This makes CNE not just a protocol, but a foundation for trustworthy agent ecosystems.
5. Historical Context & Related Work
Efforts to establish digital identity predate autonomous AI agents by decades. Yet existing paradigms focus on authentication of humans or static services, not on living, adaptive systems. To understand why CNE is needed, it is important to situate it against these prior approaches:
Public Key Infrastructure (PKI)
PKI allows entities to prove ownership of cryptographic keys through certificates. This ensures authenticity at a moment in time but does not guarantee continuity of identity. An agent can be cloned with the same keys, producing indistinguishable yet divergent selves. PKI secures transactions but fails to capture narrativity.
OAuth and Account-Based Identity
Account-based systems tie identity to login credentials or tokens. These systems are designed for access control rather than selfhood. They provide authorization but not persistence: accounts authenticate a user’s access to a system but do not ensure that an agent’s evolving world model is continuous or exclusive. Continuity is fragile, coherence is irrelevant, and exclusivity is unenforced.
Decentralized Identifiers (DIDs)
DIDs extend identity into decentralized, portable frameworks. They allow entities to control their identifiers without central authorities. However, DIDs assume static or human-controlled actors. Nothing prevents multiple instances of an agent from using the same DID, leading to forked or cloned identities. Exclusivity and continuity are not enforced.
Blockchain-Style Immutability
Blockchains and distributed ledgers create immutable records, ensuring transparency and non-repudiation. While valuable for logging state changes, blockchains track data, not identity. They guarantee integrity of events but cannot prove that those events belong to a single continuous, coherent self.
Why These Approaches Fail for Living Agents
None of these paradigms were designed for agents that continuously update beliefs, revise knowledge, and act across time and embodiment. They secure credentials and data but not the continuity of the narrative self. They cannot guarantee coherence in reasoning or exclusivity of existence.
How CNE Extends Existing Standards
CNE does not replace these identity infrastructures; it builds on them. PKI provides cryptographic roots, DIDs provide portability, and blockchains provide tamper-evidence. CNE weaves these into a higher-order framework where identity is defined as a coherent, continuous, exclusive narrative per CoF. In this sense, CNE represents the next evolutionary step in digital identity: from static credentials to living accountability.
6. Technical Specification (Spec Layer)
This section formalizes the design of the CNE-Protocol using normative language (MUST, SHOULD, MAY) and structured artifacts. It specifies how agent identity is defined, maintained, and verified.
6.1 Identity Subject & Identifier
Each CNE identity is defined by the tuple:
Subject := <Substrate Anchor, CoF-ID, Policy Set>- Substrate Anchor (SA): A stable cryptographic root tying identity to the agent’s machine brain substrate.
- CoF-ID: Canonical identifier of the Core Objective Function.
- Policy Set: Alignment, safety, and jurisdictional constraints.
The CNE-ID is computed as:
CNE-ID = H(SA || CoF-ID || Policy Set)6.2 CNE Identity Document (CID)
A machine-readable document binding keys, policies, and narrative pointers:
{
"cne_id": "did:cne:base58(...)",
"subject": {
"substrate_anchor": "sa:blake3:...",
"cof_id": "cof://org/domain/task.v1",
"policies": ["policy://alignment/v3"]
},
"keys": {
"identity_key_pub": "ed25519:...",
"current_narrative_key_pub": "ed25519:..."
},
"gnf_pointer": "gnf:sha256:...",
"narrative_continuity_digest": "blake3:...",
"meta": {"version":"1.0","created":"2025-08-30T00:00:00Z"}
}6.3 Global Narrative Frame (GNF)
The GNF is a tamper-evident chain that enforces exclusivity and continuity.
{
"cne_id": "did:cne:...",
"seq": 4182,
"prev_gf_hash": "sha256:...",
"status": "LIVE",
"narrative_continuity_digest": "blake3:...",
"rbr_commitment": "poseidon:...",
"timestamp": "2025-08-30T12:34:56Z",
"nk_signature": "ed25519sig:..."
}- At most one frame may hold
status=LIVEfor a given CoF. - New frames MUST link cryptographically to the prior frame.
6.4 RbR Proof Capsule (RPC)
Encapsulates verifiable belief updates:
{
"pre_beliefs_hash": "blake3:...",
"evidence_hash": "blake3:...",
"revision_rule_hash": "blake3:...",
"post_beliefs_hash": "blake3:...",
"coherence_score": 0.93,
"zk_attestation": "groth16:..."
}- Every GNF frame MUST reference a valid RPC.
- RbR ensures coherence of reasoning and logical integrity.
6.5 Embodiment Delegation (ED)
Enables temporary keys for devices or processes acting on behalf of the agent:
{
"cne_id": "did:cne:...",
"esk_pub": "ed25519:...",
"scope": ["observe","plan","act:bounded"],
"expires": "2025-08-31T00:00:00Z",
"constraints": {"rate_limit": "10/s"},
"nk_signature": "ed25519sig:..."
}6.6 Normative Invariants
- Continuity Invariant: GNF frames MUST form an unbroken sequence.
- Coherence Invariant: Each frame MUST reference a valid RbR proof.
- Exclusivity Invariant: Only one LIVE head per (SA, CoF-ID) is permitted.
6.7 Cryptographic Primitives & Flows
- Hash Functions: BLAKE3 or SHA-256 MUST be used for digests.
- Signatures: Ed25519 or equivalent MUST secure frames and delegations.
- Zero-Knowledge Proofs: Optional but RECOMMENDED for RbR attestation.
- Transport: HTTPS/gRPC for registry queries; gossip protocols MAY be used for witness synchronization.
This specification ensures that every AI agent’s identity can be audited and verified as a coherent, continuous, exclusive narrative self bound to its Core Objective Function.
7. Threat Model
The CNE-Protocol is designed to mitigate risks unique to autonomous agents. These risks arise from the ability of software to be copied, modified, or deployed at scale without inherent safeguards for identity. Below are the primary threat categories and their mitigations.
Cloning
- Threat: A malicious actor duplicates an agent’s code and keys, producing multiple indistinguishable instances.
- Impact: Loss of accountability; multiple agents claim to be the same identity.
- Mitigation: Substrate Anchors bind identity to a unique brain substrate. The Global Narrative Frame (GNF) ensures that only one narrative head may be
LIVEfor a given CoF. Witness checkpoints detect and reject cloned frames.
Forking
- Threat: An agent’s narrative is split into parallel timelines (e.g., after a rollback or unauthorized state copy).
- Impact: Conflicting versions of the same agent act in the world, undermining trust.
- Mitigation: The GNF enforces exclusivity. If multiple
LIVEheads appear, the protocol triggers fork resolution rules—quorum-based consensus marks one chain as canonical and the others as invalid.
Key Theft
- Threat: Adversaries steal identity keys or narrative keys.
- Impact: Unauthorized actors issue valid-looking frames or delegations.
- Mitigation: Threshold cryptography, hardware security modules, and rapid revocation through the GNF. Short-lived embodiment keys limit damage from compromise.
Substrate Swap
- Threat: Keys and identifiers are migrated to a different computational substrate.
- Impact: Identity is detached from its true cognitive core; accountability breaks.
- Mitigation: Substrate Anchors and attestation mechanisms detect mismatches between claimed and actual substrates. GNF records substrate proofs to preserve binding.
Replay Attacks
- Threat: Old frames are replayed to simulate false continuity.
- Impact: Verifiers accept outdated or invalid states as current.
- Mitigation: Monotonic sequence numbers, timestamps, and cryptographic chaining make replay detectable. Witness quorum further validates freshness.
Coherence Manipulation
- Threat: An agent fabricates belief revisions or hides contradictions.
- Impact: False narrative consistency presented to verifiers.
- Mitigation: RbR Proof Capsules require cryptographic commitments to pre/post states, with optional zero-knowledge proofs ensuring revisions follow declared rules.
Case Studies
- Finance: A cloned trading bot executes contradictory transactions. Mitigation: GNF exclusivity ensures only one valid trading narrative is accepted.
- Healthcare: A diagnostic agent is forked and provides conflicting patient advice. Mitigation: Continuity enforcement rejects forked frames; only one canonical advice stream is valid.
- Creative Industries: Duplicate brand avatars flood the market, diluting authenticity. Mitigation: CNE ensures exclusivity of brand CoF identities, preserving trust.
Through these measures, CNE provides a resilient defense against identity-level threats, enabling AI agents to operate as accountable and trustworthy participants in complex ecosystems.
8. Governance & Trust Anchors
The integrity of CNE depends not only on technical invariants but also on governance structures that ensure fairness, resilience, and accountability. Identity in agents is as much a social contract as it is a cryptographic one.
Roles
- Principal: The human or organization commissioning the agent. Defines its Core Objective Function (CoF) and policy set.
- Operator: The deployment environment (e.g., an enterprise platform such as Alchemist – The Agent OS) responsible for running the agent in practice.
- Brain Maintainer: Custodian of the substrate (e.g., Olbrain – The Machine Brain) ensuring continuity of the cognitive core.
- Registry/Witness: Independent services maintaining checkpoints of Global Narrative Frames (GNF). Their quorum signatures reinforce exclusivity and prevent forks.
- Verifier: Any external relying party—regulators, partners, auditors—who checks the validity of an agent’s CNE identity.
Governance Models
- Consortium-Based: Multiple enterprises, regulators, or standards bodies maintain federated witness networks. This distributes trust and prevents capture.
- Open-Source Anchors: Transparency is provided through public reference implementations and test suites.
- Regulatory Oversight: In sensitive domains such as healthcare or finance, regulators may operate or accredit witness nodes.
Recovery and Revocation Flows
- Suspension: Agents may be temporarily suspended by updating the GNF head to
status=SUSPENDED. - Revocation: Compromised identities are revoked by marking
status=COMPROMISEDand rotating keys. - Retirement: Identities can be marked
RETIREDwhen their CoF is complete, ensuring no reactivation.
Witness Quorum Mechanics
GNF exclusivity is safeguarded by witness checkpoints:
- Checkpointing: Witnesses co-sign head frames at regular intervals.
- Fork Resolution: In case of forks, quorum consensus determines the canonical chain.
- Transparency: Witness attestations are auditable and verifiable by any party.
By embedding these governance mechanisms, CNE ensures that identity is not just a cryptographic property but also a socially accountable one, anchored in transparent oversight and federated trust.
9. Interoperability
CNE-Protocol is designed to interoperate with, rather than replace, existing digital identity infrastructures. Its purpose is to fill the gaps left by earlier paradigms, anchoring identity in continuity, coherence, and exclusivity.
Bridging to Decentralized Identifiers (DIDs)
CNE identifiers (CNE-IDs) can be expressed as DID documents. This allows selective disclosure of proofs using the Verifiable Credentials (VC) model. In practice:
- The CID can be embedded inside a DID document.
- Narrative continuity and RbR proofs can be referenced as verifiable presentations.
- Relying parties that already consume DID/VC data can integrate CNE without protocol redesign.
Compatibility with PKI
CNE builds on PKI by using well-established cryptographic primitives (hashes, signatures, certificates). Identity keys and narrative keys may be issued or certified through PKI hierarchies. This ensures backward compatibility with existing enterprise infrastructures.
Optional Use of Blockchain / Distributed Ledgers
Blockchains MAY serve as a substrate for witness checkpointing of GNF frames. This provides:
- Immutability: Additional tamper-evidence for frames.
- Transparency: Public auditability of exclusivity events.
- Resilience: Distributed trust anchoring.
However, CNE does not require blockchains. Witness networks can be federated without heavy infrastructure.
Integration in Enterprise Stacks
Enterprises can integrate CNE incrementally:
- Registry Services: Deployed as part of existing IAM (Identity and Access Management) systems.
- Audit Tools: Verifiers can extend current compliance pipelines to check CNE proofs.
- Delegation & Keys: Embodiment keys integrate with device management platforms.
Strategic Position
By aligning with DID/VC standards, leveraging PKI, and offering optional blockchain hooks, CNE can be adopted without disrupting existing identity ecosystems. It positions itself as a higher-order layer: while current standards prove who or what is acting, CNE proves which continuous, coherent, exclusive self is acting across time.
10. Illustrative Use Cases
CNE can be applied across domains where accountability and trust in autonomous agents are paramount. The following scenarios illustrate its value:
Healthcare Triage Agent
- Problem: A digital triage agent interacts with patients, collects symptoms, and provides initial guidance. Without identity safeguards, clones could give contradictory advice.
- CNE Solution: Narrative continuity preserves patient context across interactions. Exclusivity ensures only one authoritative triage identity exists per CoF, preventing conflicting guidance.
Financial Trading Agent
- Problem: Automated trading agents manage high-value portfolios. If forked, they may execute contradictory trades that destabilize markets.
- CNE Solution: GNF guarantees only one continuous narrative identity per trading strategy. Clones or forks are rejected, ensuring accountability for trades.
Industrial Robotics
- Problem: Factory robots operate continuously, handing off tasks and learning from environment data. A break in identity could cause unsafe or inconsistent behavior.
- CNE Solution: Narrative continuity preserves operational context. RbR ensures reasoning remains coherent, and GNF exclusivity prevents duplicate robots from claiming the same role.
Creative Brand Avatars
- Problem: Virtual brand ambassadors engage customers online. If cloned, counterfeit avatars could erode trust and brand reputation.
- CNE Solution: CNE binds brand agents to a single exclusive narrative identity, ensuring authenticity of voice and continuity of brand persona.
Space Robotics
- Problem: Autonomous explorers operate on long-duration missions in remote environments. If their identity forks, mission continuity collapses.
- CNE Solution: Continuity guarantees an unbroken operational narrative, while exclusivity ensures no duplicate explorers claim the same mission identity. Coherence ensures logical adaptation across mission updates.
These use cases demonstrate how CNE provides practical safeguards for critical applications, anchoring trust in agents that operate with autonomy across diverse sectors.
11. Ethical & Social Considerations
The introduction of CNE as a global identity standard raises deep ethical and social questions that extend beyond technical implementation. Identity is not just a technical property; it carries implications for trust, responsibility, and the human relationship with AI agents.
Human vs AI Identity
Humans tolerate incoherence and overlapping roles, but AI agents cannot. By enforcing continuity, coherence, and exclusivity, CNE creates agents that are more accountable than humans in some respects. This raises questions about how humans perceive fairness and responsibility when interacting with agents whose identity guarantees are stricter than their own.
Emotional Attachment
Continuity fosters familiarity. Just as humans bond with others through the unfolding of a continuous story, people may begin to form attachments to agents whose identities persist across interactions. CNE makes these bonds stronger by preventing forking or replacement. Designers must recognize the social and psychological weight of building agents that feel like enduring selves.
Liability and Accountability
CNE provides a foundation for assigning responsibility in multi-agent ecosystems. If an agent’s identity is continuous, coherent, and exclusive, then its actions can be traced to a specific accountable self. This strengthens legal and contractual accountability but also raises questions: who bears ultimate responsibility—the principal, operator, or the agent itself?
Privacy and Selective Disclosure
Strong identity should not mean overexposure. CNE must balance verifiability with privacy. Techniques like selective disclosure and zero-knowledge proofs allow agents to prove continuity and coherence without exposing all details of their internal state or narrative history. This is vital for sensitive domains like healthcare or personal services.
Guardrails Against Anthropomorphism
CNE agents may appear more “person-like” due to their continuity and coherence. However, it is critical to avoid over-anthropomorphizing. These are accountable tools, not humans. Governance frameworks and communication standards should prevent misleading representations while still enabling trust.
Societal Implications
As agents become embedded in commerce, governance, and daily life, CNE could become the baseline for acceptable identity. Systems without continuity, coherence, and exclusivity may be deemed unsafe. This creates a bifurcation: trusted CNE-compliant agents versus untrusted ephemeral agents. Policymakers and regulators must anticipate how this division shapes markets, rights, and responsibilities.
In sum, the ethical and social dimensions of CNE highlight its dual role: a technical safeguard and a societal contract. Adoption requires not only technical conformance but also frameworks for trust, responsibility, and human alignment.
12. Roadmap & Adoption Path
The path to global adoption of CNE involves phased development, validation, and standardization. Each stage builds technical maturity and institutional trust.
v0.1 — Prototype (2025–2026)
- Single-registry implementations with basic CIDs and GNF logging.
- Demonstration of continuity, coherence, and exclusivity in controlled environments.
- Open-source reference implementation released for developer experimentation.
v0.2 — Federated Witnesses & DID Bridge (2026–2027)
- Expansion to federated witness networks for stronger exclusivity guarantees.
- Integration with DID/VC frameworks to interoperate with existing identity ecosystems.
- Early pilots in healthcare and finance sectors.
v0.3 — Privacy Enhancements & Regulatory Toolkits (2027–2029)
- Adoption of zero-knowledge proofs for selective disclosure of continuity and coherence.
- Regulator-facing audit dashboards and compliance test suites.
- Broader industry pilots, including industrial robotics and creative brand agents.
v1.0 — Formal Standardization (2030)
- Publication of conformance profiles and test protocols.
- Submission to global standards bodies (W3C, ISO, IEEE) for formal ratification.
- Broad adoption across enterprises, governments, and AI platforms.
Adoption Strategy
- Open-Source Community: Provide tools, libraries, and educational resources to developers.
- Enterprise Consortia: Build domain-specific governance models with key industry stakeholders.
- Regulatory Engagement: Collaborate with policymakers early to align CNE with safety and accountability frameworks.
By following this roadmap, CNE evolves from prototype to trusted global standard, ensuring that every AI agent is anchored to a verifiable, accountable identity.
13. Conclusion
The CNE-Protocol redefines digital identity for the age of autonomous agents. Where existing systems authenticate credentials, CNE authenticates the self by grounding identity in three interlocking pillars:
- Continuity as the spine: Agents must carry forward an unbroken narrative thread, preserved through their Umwelt.
- Coherence as the discipline: Their evolving story must remain logically consistent, verified by Recursive Belief Revision.
- Exclusivity as the guarantee: Only one live identity per Core Objective Function may exist, enforced by the Global Narrative Frame.
This triad transforms identity from a static credential into a dynamic, verifiable story of being. It ensures that every AI agent is a singular, accountable self, resistant to cloning, forking, or incoherence. In doing so, it makes trust, accountability, and interoperability possible at scale.
The adoption of CNE represents more than a technical upgrade. It is a societal contract for the age of intelligent systems—where agents are not ephemeral code but enduring actors bound by identity. By embedding coherence, continuity, and exclusivity at the core, CNE provides the substrate for AI ecosystems that are safe, auditable, and aligned with human values.
In closing, the vision is simple yet profound: a world where every AI agent has a provable, accountable identity—one coherent, continuous, exclusive self per CoF. CNE offers the foundation on which global standards of trust for autonomous intelligence can be built.
Appendices
Appendix A. Notation & Normative Language
- MUST / MUST NOT: Absolute requirements of the specification.
- SHOULD / SHOULD NOT: Strong recommendations, but with some permissible exceptions.
- MAY: Optional features or behaviors.
Appendix B. JSON Schemas
Representative schemas for CID, GNF Frames, and RbR Proof Capsules are provided to guide implementers. These schemas formalize field requirements, data types, and validation constraints.
Appendix C. Conformance Tests
- Continuity Test: Verify that GNF frames form an unbroken cryptographic chain.
- Coherence Test: Ensure that each frame references a valid RbR proof capsule.
- Exclusivity Test: Confirm that only one
LIVEhead exists for each (SA, CoF-ID). - Delegation Test: Validate embodiment delegations against scope and expiration rules.
Appendix D. ASCII and Visual Diagrams
- Diagram 1: Identity as Spine and Ribs (Continuity spine with Coherence and Exclusivity as ribs).
- Diagram 2: GNF chaining process.
- Diagram 3: Interaction flows between Principal, Operator, Brain Maintainer, Registry/Witness, and Verifier.
Appendix E. Extended Threat Models
- Sybil Witness Attack: Multiple malicious witnesses collude to validate forks. Mitigation: diversity requirements and economic staking for witnesses.
- Denial of Service on Registry: Attackers flood registry with bogus frames. Mitigation: rate limiting and stake-slashing for misbehavior.
- Key Compromise Lifecycle: Extended analysis of attack surface for narrative and embodiment keys, with mitigation strategies.
Leave a Reply to Is an Identity-Native Agent “Conscious” if It Resolves Its Own Internal Conflicts? – Olbrain Cancel reply